VirtualBox: How to compile Linux Kernel on a Debian Guest
C. BinKadal
---
Sendirian, Berhad
Debian Packages
- See https://doit.vlsm.org/026.html#idx02 for more details.
Download Latest STABLE Kernel
- Fetch the latest STABLE kernel from https://kernel.org/.
# START =============================================================
# VARIABLES
STABLE=$(wget -O - -o /dev/null https://www.kernel.org/finger_banner | awk '/stable/ {print $NF; exit}')
MAJOR=$(echo $STABLE | cut -d. -f1)
URL="https://kernel.org/pub/linux/kernel/v$MAJOR.x"
KERNEL="linux-$STABLE.tar.xz"
TARBALL="linux-$STABLE.tar"
PGP="linux-$STABLE.tar.sign"
KURL="$URL/$KERNEL"
PURL="$URL/$PGP"
# ===================================================================
# Download the latest stable kernel tarball
wget -c $KURL
# ===================================================================
# Download the signature
wget -c $PURL
# ===================================================================
# Locate and import the PGP keys for verification
gpg --locate-keys torvalds@kernel.org gregkh@kernel.org
Sign Key (optional)
gpg --sign-key gregkh@kernel.org
Uncompress the file and verify
# ===================================================================
# Uncompress the kernel tarball
unxz $KERNEL
# Verify the tarball signature
gpg --verify $PGP $TARBALL
Extract TAR file
# ===================================================================
# Extract the kernel tarball
tar xvf $TARBALL
# ===================================================================
# Enter the kernel source directory
cd linux-$STABLE
Overkilled Cleaning Habit
Once in a while, someone will ask about why not “make distclean,” or “make mrproper,” or “make clean.” Ok, this is the way! ℼ
make distclean; make mrproper; make clean;
AMD64 Option 1: Reusing “.config” files
- If copying a wrong “.config” file,
you might create a massive kernel with huge modules.
- Consider copying a working “.config” file from the “/boot/” directory.
- Or, try to download this “.config” file
- See also Linux/AMD64 Kernel Config for VirtualBox.
- Or, try to reuse any .config file. ℼ
- Run:
yes "" | make oldconfig
AMD64 OPTION 2: A “.config” file from scratch
- If OPTION 1 failed, consider making a “.config” file from scratch with:
make x86_64_defconfig
yes "" | make oldconfig
Menuconfig
make menuconfig
E.g., for cbkadal
General setup --->
(-cbkadal-10) Local version - append to kernel release
Kernel compression mode (XZ) --->
(cbkadal) Default hostname
<*> Kernel .config support
[*] Enable access to .config through /proc/config.gz
<*> Enable kernel headers through /sys/kernel/kheaders.tar.xz
Processor type and features --->
[ ] EFI runtime service support
[*] Enable loadable module support --->
[*] Module unloading
[*] Forced module unloading
[*] Module versioning support
File systems --->
<*> FUSE (Filesystem in Userspace) support
<*> Character device in Userspace support
<*> Virtio Filesystem
Security options --->
[ ] NSA SELinux Support
[*] AppArmor support
[*] Enable introspection of sha1 hashes for loaded profiles
[*] Enable policy hash introspection by default
First legacy 'major LSM' to be initialized
(X) AppArmor
Kernel hacking --->
printk and dmesg option --->
[*] Enable dynamic printk() support
Compile-time checks and compiler options --->
[*] Install uapi headers to usr/include
Compile (make)
time make
- FYI Compile Time: ℼ
- (Linux) Intel(R) Core(TM) i5-9400F CPU @ 2.90GHz
- real 3m5.825s
- user 14m51.339s
- sys 1m59.721s
- (Windows 10) Intel(R) Core(TM) i5-9400F CPU @ 2.90GHz
- real 4m17.702s
- user 21m29.718s
- sys 2m21.400s
- (Linux) Lenovo E135 (AMD E2-2000 APU with Radeon(tm) HD Graphics)
- real 123m25,746s
- user 211m58,046s
- sys 28m1,298s
- (Linux) Lenovo Yoga 300 (Intel(R) Celeron(R) CPU N2840 @2.16GHz)
- real 69m6,574s
- user 115m1,006s
- sys 19m12,436s
- (Windows 10) Lenovo Yoga 300 (Intel(R) Celeron(R) CPU N2840 @2.16GHz)
- real 4580m11.804s (Yes, there is something wrong here!)
- user 6900m36.555s
- sys 864m34.820s
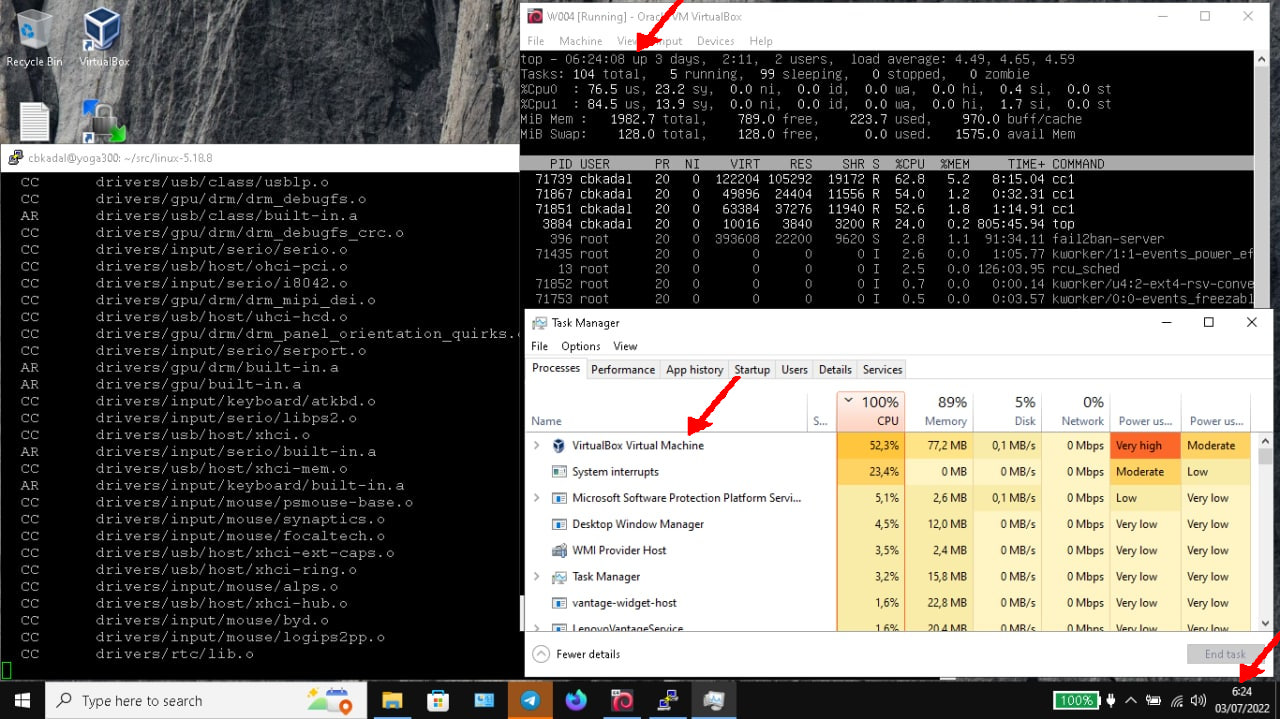
- One More Time (after fixing the Windows 10 drivers):
- real 72m26.981s
- user 114m32.041s
- sys 24m54.993s
- One More Time (after fixing the Windows 10 drivers):
- (Linux) Intel(R) Core(TM) i5-9400F CPU @ 2.90GHz
Install
- Use sudo ℼ
# USER: ROOT ============
# Install the modules
sudo make modules_install
# Install the kernel
sudo make install
# Install the headers
sudo make headers_install INSTALL_HDR_PATH=/usr
Cleaning
You need to keep some parts of the Linux kernel source. You can delete the rest.
make clean
rm -rf arch/[a-u]* arch/xtensa/ block/ certs/ crypto/ Documentation/
rm -rf drivers/ fs/ init/ io_uring/ ipc/ kernel/ lib/ lib/
rm -rf mm/ net/ rust/ samples/ security/ sound/ virt/ usr/
Linux Firmware
- URL: https://git.kernel.org/pub/scm/linux/kernel/git/firmware/linux-firmware.git/
- E.g. TARBALL “linux-firmware-20220509.tar.gz”
- open the TARBALL
- Go to folder “linux-firmware-20220509/”
- Copy the missing modules into “/lib/firmware/”. E.g. (ROOT),
- E.g. TARBALL “linux-firmware-20220509.tar.gz”
cp -r i915/ /lib/firmware/
cp -r tigon/ /lib/firmware/
cp -r e100/ /lib/firmware/
cp -r rtl_nic/ /lib/firmware/
Old Modules
- You have to delete old modules (/lib/modules) and old config (/boot/) files manually. Do not forget to “update-grub”.
- Visit (ROOT):
cd /lib/modules/
ls -al
cd /boot/
ls -al
Table of Content
- VirtualBox
- UTM MacOS Silicon
- Debian Guest
- Setup a Debian Guest
- More
- Windows PowerShell and Terminal
- Start, Shutdown, Login and Logout
- Passing PASTE
- SCP
- Substitue (su) ROOT
- sources.list
- Installing Debian Packages
- ROOT .vimrc and .profile
- ADDUSER
- HOSTNAME
- USER .vimrc and .bash_aliases
- Locales
- Boot Recovery Mode
- Universally Unique Identifier (UUID)
- Simple Linux Scripts
- Troubleshooting
- GitHub
- GNUPG
- More Links
© 2021-2024 --- C. BinKadal ---
About ---
Revision: Tue 26 Nov 2024 18:00.